Continuously Identify, Validate, and Prioritize Exposures
Continuous Threat Exposure Management (CTEM), Operationalized
Continuous Threat Exposure Management (CTEM) is a framework for continuously identifying, validating, prioritizing, and reducing real-world security exposure. It shifts security teams from periodic scanning to ongoing risk reduction — focusing on what is actually exploitable and impactful.
Implementing CTEM at Scale
The Challenges of CTEM, and What It Takes to Power It
The Brinqa Solution
How Brinqa Powers a CTEM Strategy

The Brinqa Solution
How Brinqa Powers a CTEM Strategy
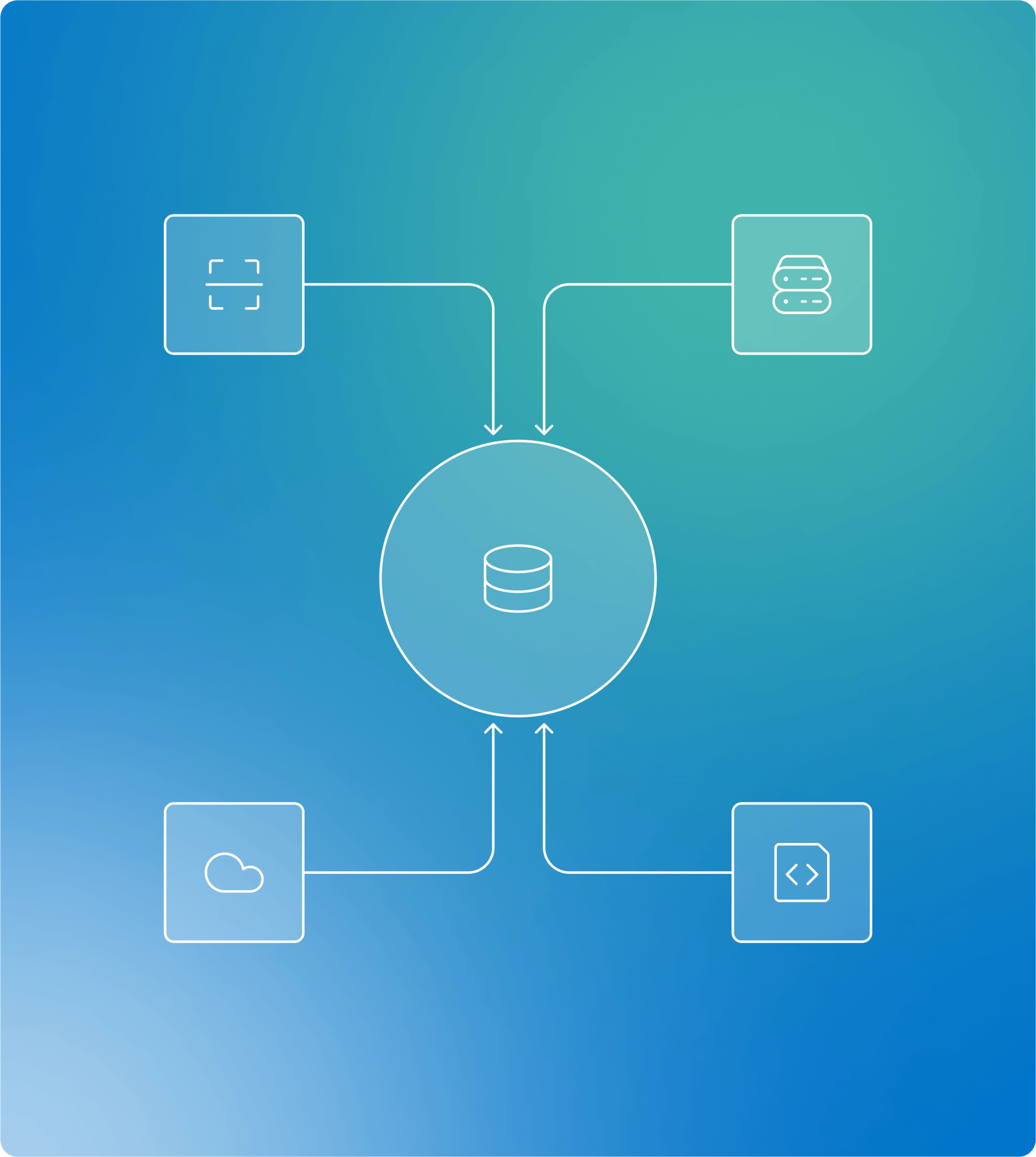
Brinqa operationalizes CTEM by connecting the tools teams already use into a single, data-driven platform. With 240+ out-of-the-box integrations, Brinqa brings together asset, vulnerability, threat, and business data to give teams deeper visibility, richer context, and a clearer view of real exposure.
By using more of this data—not just isolated findings—Brinqa correlates signals across sources to support better decisions and faster, more targeted remediation. Teams maximize the value of existing security investments while moving CTEM from a framework into a repeatable, scalable practice.
How Brinqa Works
Orchestrating Risk Reduction Across the CTEM Lifecycle
Scoping & Discovery:
The Data Layer continuously ingests and correlates exposure data across your entire environment, maintaining the complete asset inventory and relationship mapping CTEM programs require. The CyberRisk Graph™ enables accurate scoping of what needs protection and continuous discovery of new exposures.
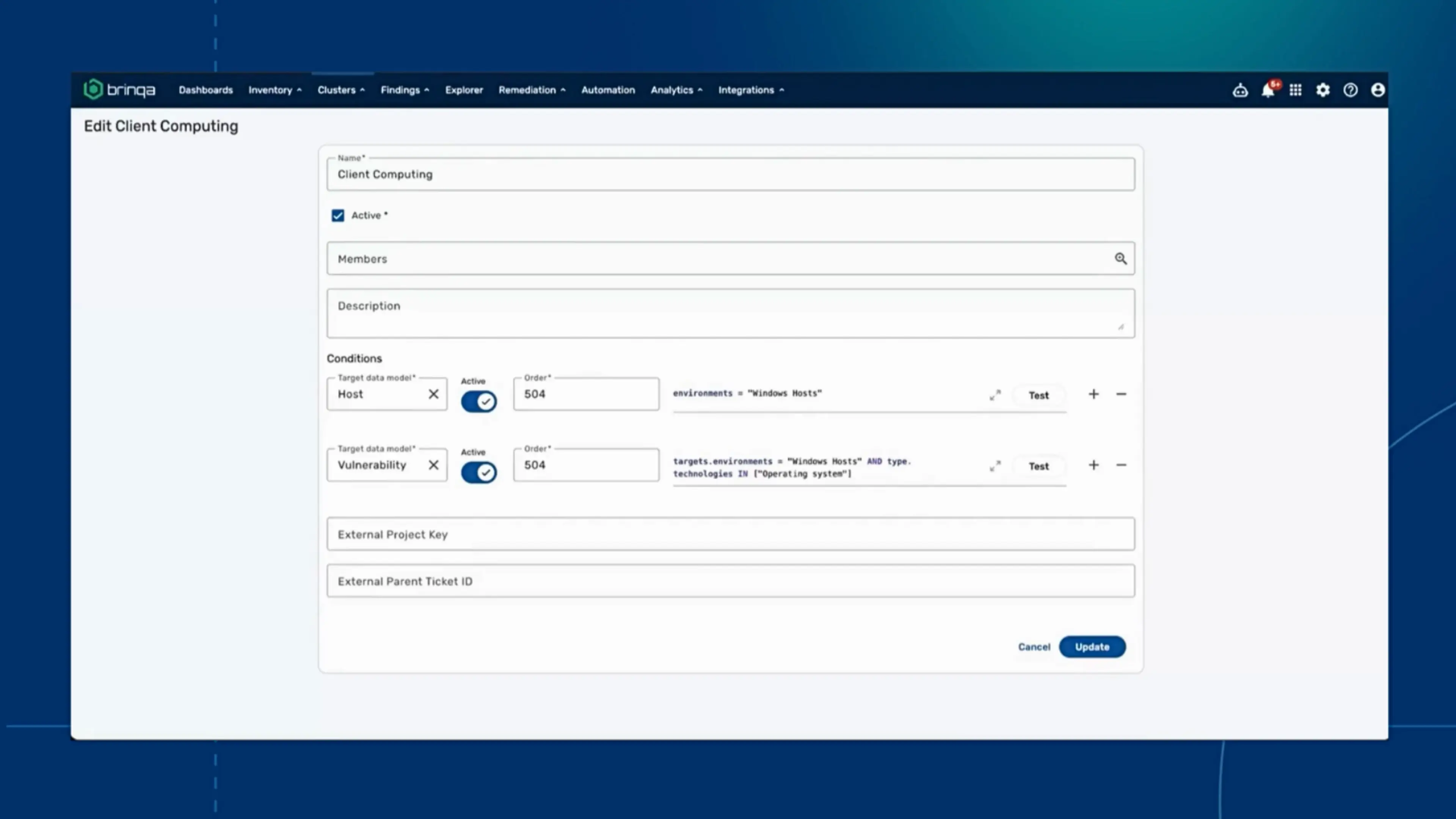
Identify & Target Remediation Owners
See how Brinqa operationalizes mobilization
Watch how Brinqa automatically assigns remediation ownership at the layer level — turning CTEM’s mobilization stage into coordinated action across teams.
Why Brinqa
Discover Key Features That Deliver an Enterprise Level Strategic Edge
Understanding CTEM
CTEM, Explained
CTEM brings structure and continuity to how organizations manage exposure, turning fragmented security data into continuous, prioritized action.

- Scope → define what to evaluate
- Discover → identify vulnerabilities and exposures
- Prioritize → focus on real risk, not just severity
- Validate → confirm what’s actually exploitable
- Mobilize → drive and track remediation
Result: Continuous, risk-driven reduction—not periodic assessment.
Customer Success Stories
Proven Enterprise Outcomes
Brinqa at Work
Solutions For Every Member of Your Vulnerability Management Program
CISOs and security risk leaders

Exposure and risk management teams

Security Operations Teams


Exposure Management
The CTEM Challenge: Too Many Tools, Not Enough Integration