Exposure Management Without Limits
Kill the Fire Drill with AI-Powered Exposure Management
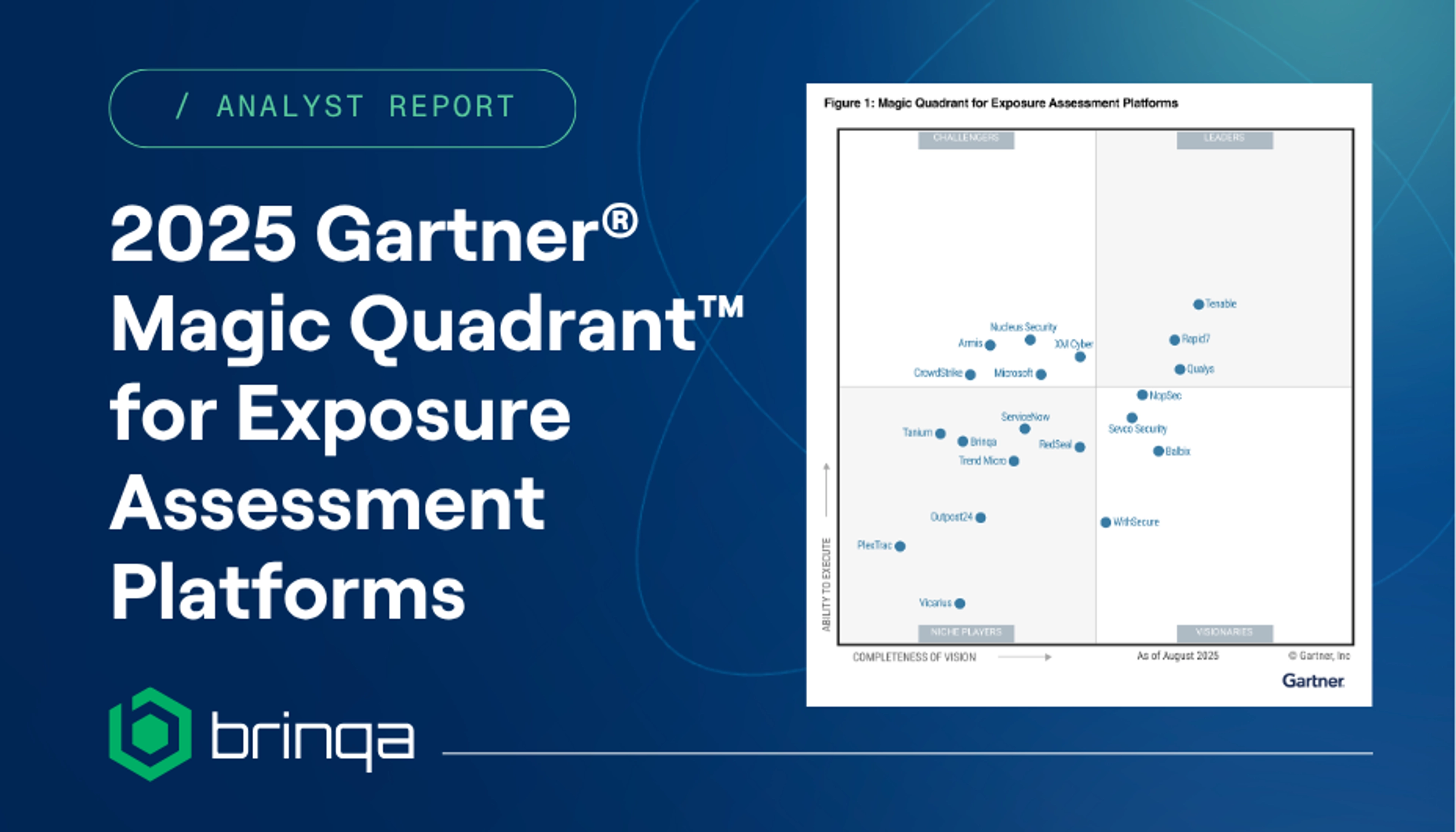
Trusted by the World’s Most Security-Conscious Enterprises













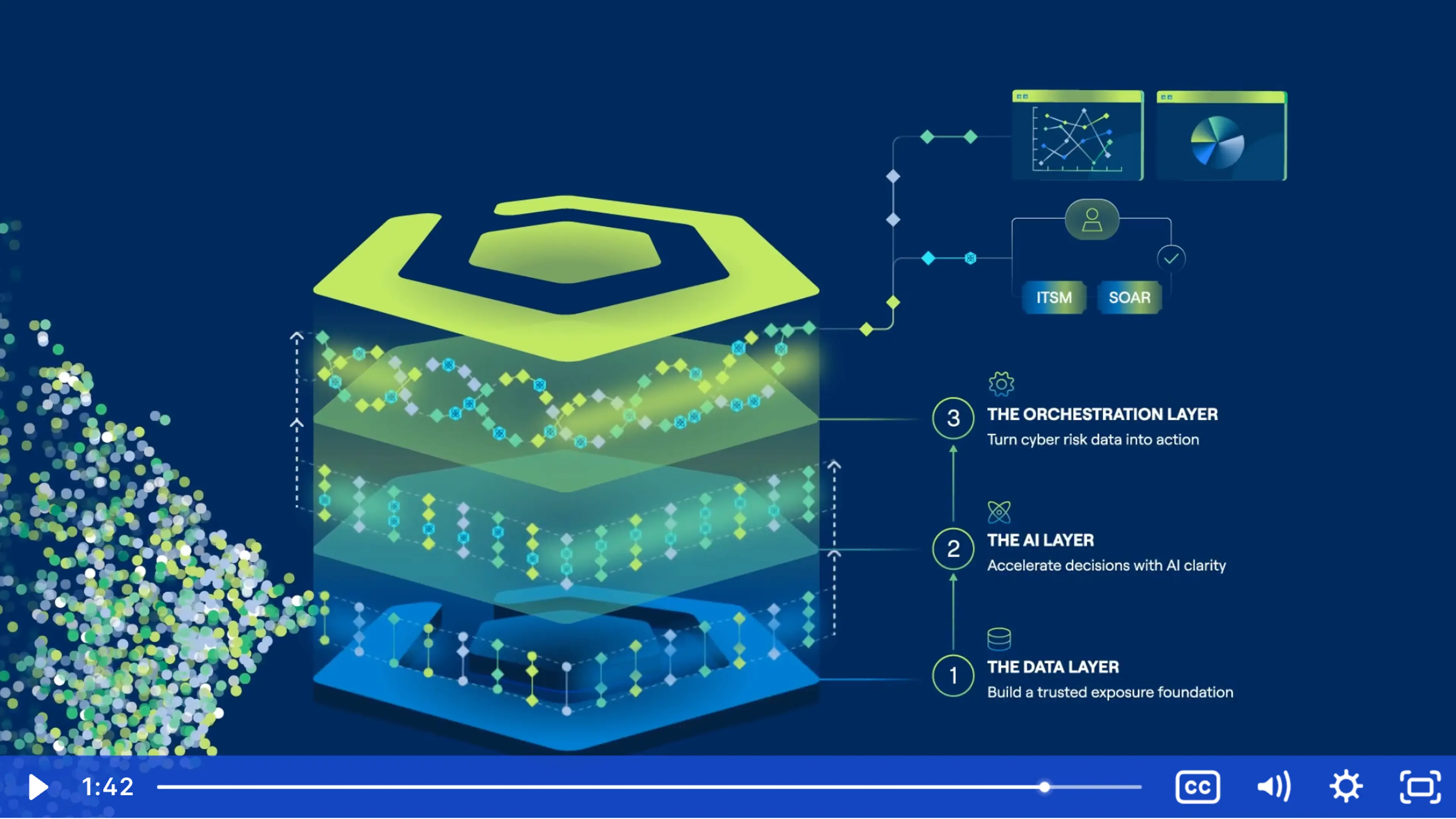
Turning Chaos into Clarity
Exposure Management for the Age of Smart Chaos
Chaos is the reality of modern enterprise environments. Brinqa brings structure to the complexity by unifying cyber risk data into a connected view of exposure that shows where risk truly exists and how to reduce it.
Why Exposure Management Matters
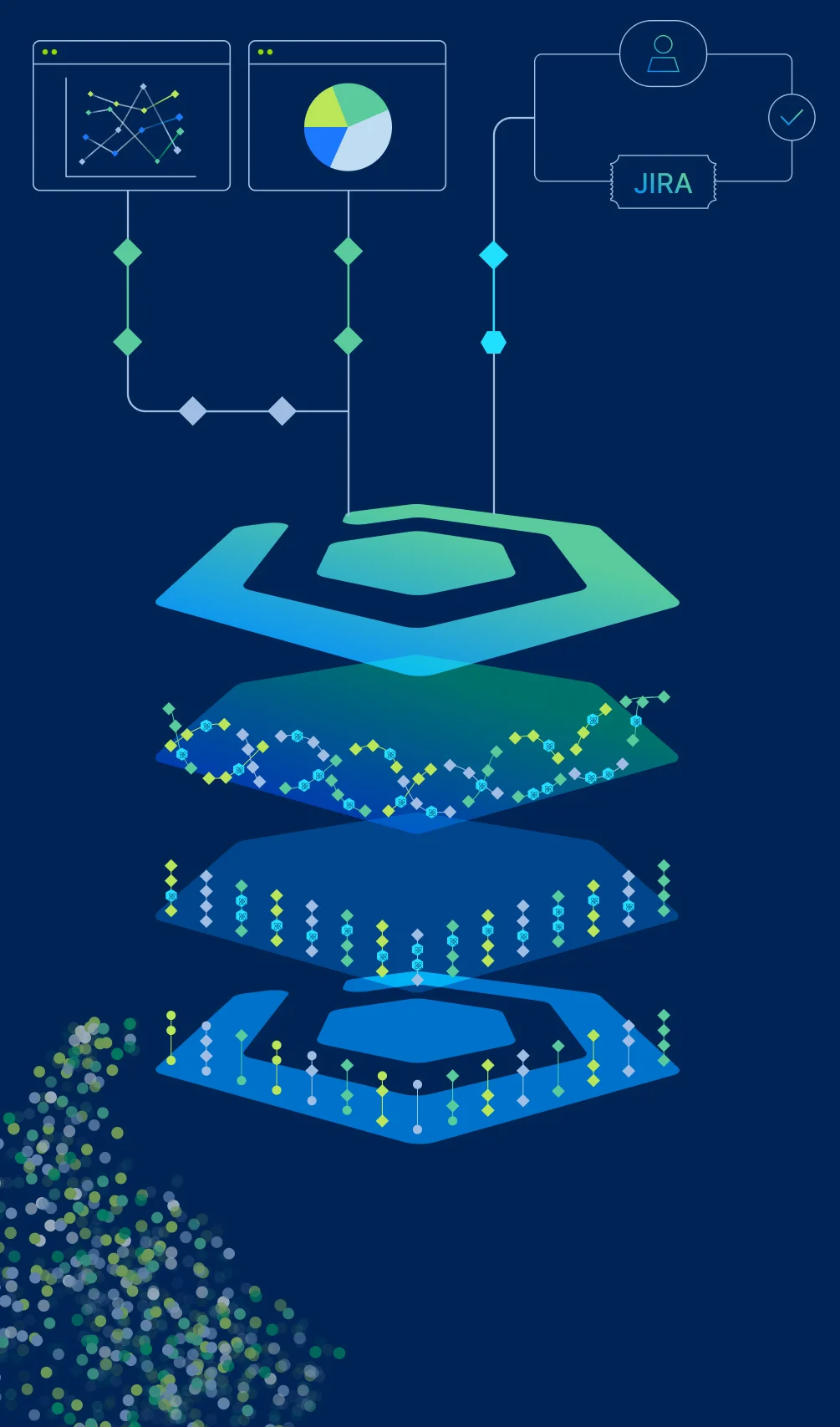
Turn Millions of Signals into Confident Action
Security chaos doesn’t start with a lack of tools – it starts with disconnected data. Vulnerabilities, cloud findings, application risks, identities, and assets all generate signals, but without structure and context, teams are left reacting instead of reducing exposure.
Brinqa brings order to that chaos. By unifying exposure data and embedding AI across the exposure management lifecycle, our platform helps teams prioritize with confidence, remediate faster, and clearly communicate progress.
Who it's for
Cyber Risk & Exposure Management Solutions by Role
CISO & Security Risk Management Leaders

Vulnerability & Exposure Management Leaders

IT, Cloud, & App Security Teams

Exposure Management Solutions for Complex Enterprises
Built for the Real World to Reduce Risk, Strengthen Compliance, and Build Confidence.
- Learn More
Retail
Brinqa empowers retailers to secure omnichannel operations and protect customer data with PCI DSS–aligned, data-driven exposure management.
Manufacturing
Brinqa helps manufacturers protect production-critical environments with unified IT and OT exposure visibility, risk-based prioritization, and compliance alignment across NIST SP 800-53, ISO 27001, and GDPR.
- Learn More
Banking
Brinqa gives banks data-driven clarity on exposures that affect customer trust and compliance, unifying risk data across frameworks like NIST SP 800-53, PCI DSS, and GDPR.
- Learn More
Finance
Brinqa enables financial organizations to centralize cyber risk data and maintain NIST SP 800-53, ISO 27001, and GDPR compliance with unified, data-driven exposure management.
- Learn More
Insurance
Brinqa helps insurers protect policyholder data and streamline HIPAA, GDPR, and NIST SP 800-53 compliance across distributed environments – both on-premises and in the cloud.
- Learn More
Technology
Brinqa enables technology and SaaS companies to secure software supply chains and maintain SOC 2 and GDPR compliance from code to cloud.
- Learn More
Utilities
Brinqa supports critical infrastructure providers with unified IT and OT visibility to ensure compliance with NIST SP 800-53, EU CRA, GDPR, and industry resilience standards.
"We more than doubled our InfoSec team’s productivity with Brinqa while improving visibility across our entire business."
Mohamed Toka, CISO