Unified Exposure Management
See How the Brinqa Platform Works
Every scanner, every cloud environment, every ticketing system produces data. The problem isn't having too much of it, it's that most of it is fragmented, duplicated, and disconnected from the risks that actually matter. See how Brinqa changes that.
The Problem
The data isn't the problem. It's what gets lost inside it.

The Problem
The data isn't the problem. It's what gets lost inside it.
In most enterprise environments, more than 78% of assets have no defined owner.* The same finding gets reported five different ways across three different tools. Security teams spend hours reconciling what is fundamentally the same issue. That's not security work. That's spreadsheet archaeology.
The risk is real. The accountability isn't.
The Solution
A program built to operate inside the chaos, not around it.
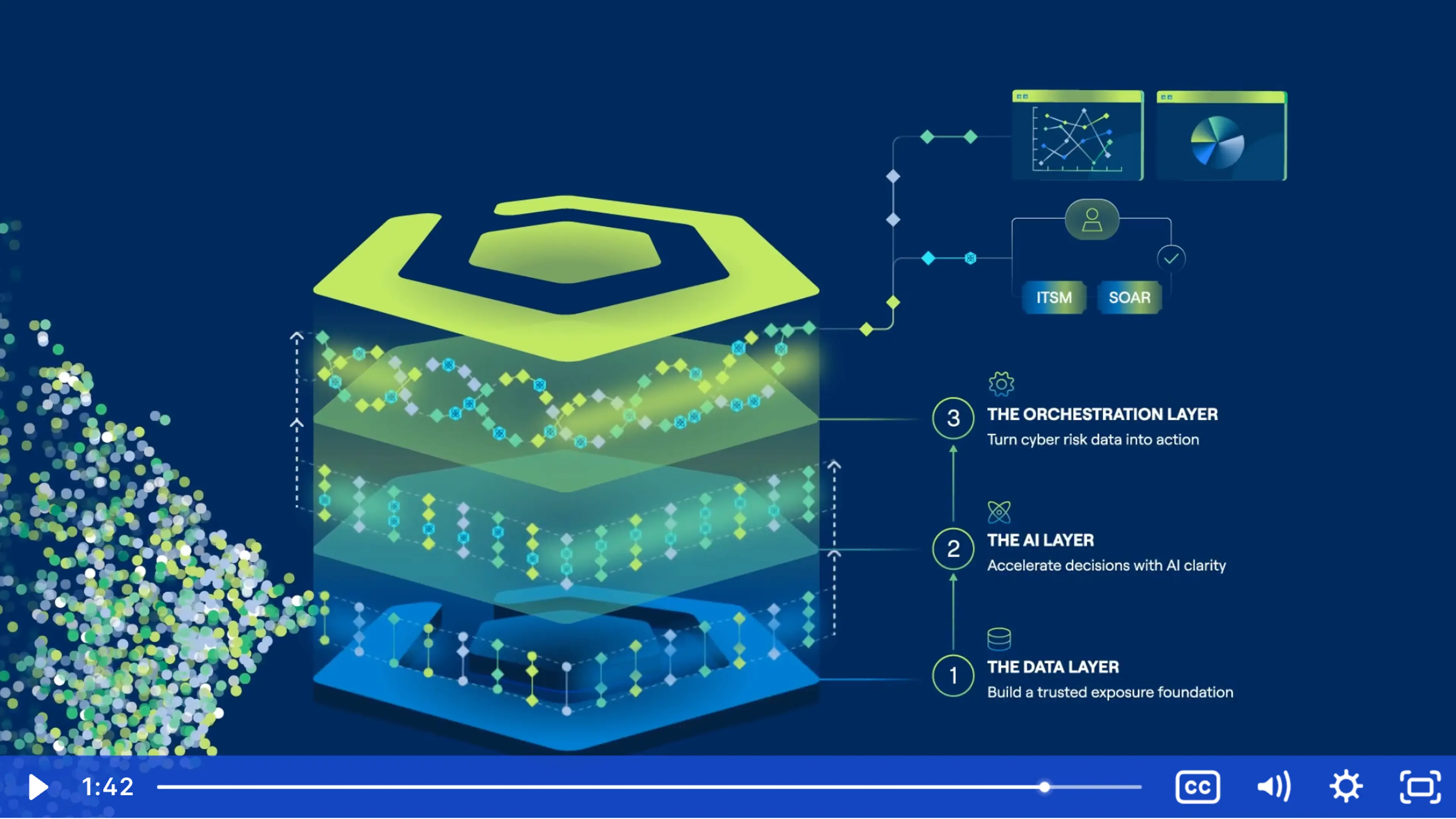
The answer to exposure management chaos isn't more dashboards or more tools. It's a platform that can ingest every signal, normalize the noise, establish ownership, and act — automatically, at scale, without losing the context that makes prioritization meaningful. That's what Brinqa does.
Deduplicate at scale
Thousands of overlapping findings collapse into single, actionable records — so your team is working the real list, not an inflated one.
Establish ownership automatically
Every risk finds an owner. No manual triage. No guesswork. AI-driven attribution connects findings to the right teams from the start.
Prioritize by what matters to the business
Cyber risk prioritization grounded in confirmed exploitability and business impact, not CVSS scores alone.
Take action without writing code
SmartFlows puts automation in your team's hands. Build, modify, and run remediation workflows visually. Your rules. Your logic.
Customer Outcomes
What Smart Chaos looks like in practice:
When exposure data is clean, correlated, and actionable, the numbers move. Here's what that looks like for Brinqa customers.

80% reduction in unassigned vulnerabilities (Nestlé Customer Case Study)
97%of risks mapped to an owner (Fortune 500 Tech Company Case Study)
2–3x improvement in vulnerability management productivity (SAP Customer Case Study)