The CTEM Challenge: Too Many Tools, Not Enough Integration

Stop us if you’ve heard this one before: A security team logs into a vulnerability scanner and sees hundreds of issues. They open a cloud security tool – different numbers. The asset inventory doesn’t match either one. Meanwhile, the attack surface keeps expanding. The result? Conflicting data, endless spreadsheets, and no clear path to action.
This is the reality for many enterprises today. Despite investing in dozens of tools, security teams still struggle to answer a simple question: Where are we most exposed right now?
Traditional vulnerability management can’t keep up because it’s fragmented and reactive. That’s where continuous threat exposure management (CTEM) steps in. As Gartner explains, CTEM “surfaces and actively prioritizes whatever most threatens your business.” CTEM integrates data from across the security stack, evaluates exposures in real time, and prioritizes them based on business impact, so teams can stop chasing noise and focus on what really matters.
But here’s the challenge: CTEM isn’t powered by a single solution. It relies on an ecosystem of technologies to continuously identify and prioritize exposures. When these tools share data and work together, they deliver a real-time, accurate picture of your threat exposure. When they don’t, you’re left with silos and noise instead of clarity.
Key CTEM Technologies and Tools
CTEM uses a combination of technologies and tools to continuously find, assess, and respond to security risks, including:
- Asset Discovery Tools
- Vulnerability Scanners
- Attack Surface Management (ASM) Tools
- Threat Intelligence Platforms Breach and Attack Simulation (BAS)
- Tools Security Orchestration, Automation, and Response (SOAR)
- Security Information and Event Management (SIEM)
- Risk-Based Vulnerability Management (RBVM)
Together, these tools offer the ability to respond faster, as well as a smarter strategy for investing time and resources. But while CTEM offers major security benefits, implementing it is not easy, especially for organizations with complex systems or limited resources.
Top Challenges of CTEM Adoption: The Security Tool Integration Gap
Many large organizations already use a wide range of security tools, but these tools often operate in silos. A vulnerability scanner might identify issues, but without access to business context or threat intelligence, it can’t accurately prioritize what matters most. Worse, it may not automatically share information with remediation teams or incident logging platforms. This lack of integration forces security teams to manually connect the dots – wasting time, increasing risk, and delaying effective response.
This complex tooling environment creates several challenges:
Incomplete Asset Visibility
CTEM depends on knowing everything in your digital environment, but many organizations have blind spots like shadow IT, forgotten cloud assets, unknown endpoints, and unmanaged code repositories. This includes custom-built applications running in CI/CD pipelines, virtualized containers spun up for short-term tasks, and cloud services deployed outside standard provisioning channels. For example, an employee might set up a personal cloud storage folder or deploy a containerized app that’s never monitored or scanned. You can’t protect what you don’t know exists. CTEM only works if it has a complete and continuously updated view of your attack surface – including all infrastructure, applications, and development artifacts.
Prioritization Overload
Security tools often generate thousands of alerts and vulnerabilities, making it difficult to determine what truly matters. CTEM must help teams cut through the noise and focus on the most impactful risks, but many organizations still rely on static CVSS scores or basic exploitability ratings that lack context. Fixing everything isn’t feasible, and without intelligent prioritization based on actual business impact and real-world threat activity, teams risk wasting time on low-impact issues while critical exposures remain unaddressed.
Lack of Skills and Resources
Running CTEM requires skilled professionals across threat analysis, vulnerability management, automation, and incident response—expertise many organizations lack. Continuous scanning, testing, and validation demand significant time, compute resources, and operational discipline. As a result, some organizations find CTEM too resource-intensive to implement fully. For example, a company may manage weekly vulnerability scans but lack the bandwidth to run daily breach simulations or automate response due to an already overburdened IT team focused on firewall maintenance and patching.
Keeping Up With Change
Systems, users, and attack techniques are constantly evolving, so CTEM must be equally dynamic. However, many organizations struggle to keep CTEM processes current amid shifting priorities and fragmented security cultures. Resistance to change, hesitation around automation, and siloed teams – especially across IT, DevOps, and security – can all hinder progress.
Successfully adopting CTEM goes beyond technology. It requires strong cross-functional collaboration and cultural alignment. Business and DevOps teams may view CTEM as intrusive or burdensome if it alters established workflows or adds perceived friction. To overcome this, security leaders must work collaboratively to build trust, align CTEM efforts with business outcomes, and embed security in a way that accelerates, not obstructs, innovation and delivery.
Costs and Licensing
An environment consisting of multiple CTEM-related tools can be expensive to maintain, especially at enterprise scale. Costs include software licenses, staff, training, infrastructure, and support. Organizations must find a balance between risk and budget—which often slows down CTEM adoption.
How to Overcome CTEM Challenges: Practical Strategies
Overcoming the challenges of implementing CTEM is absolutely possible, even for organizations with limited resources. Here are practical strategies to tackle each major challenge:
Step 1: Build Repeatable, Adaptive Processes
- Automate routine scans and updates.
- Use dashboards and trend reports to track exposures over time.
- Continuously incorporate new assets, applications, and business changes into CTEM workflows.
Step 2: Consolidate and Automate Where Possible
- Choose platforms with multiple CTEM functions to reduce tool sprawl.
- Prioritize solutions with open APIs or pre-built integrations.
- Start with high-impact integrations such as linking asset discovery with vulnerability management.
Step 3: Prioritize Asset Inventory First
- Deploy discovery tools to map your entire environment.
- Run regular scans of your external attack surface.
- Compare discovered assets against known inventories and close visibility gaps early.
Step 4: Use Risk-Based Prioritization Tools
- Implement an RBVM solution that factors in threat intelligence, asset value, and exploitability.
- Define custom risk scoring aligned to your business objectives.
- Focus remediation on vulnerabilities affecting mission-critical systems first.
How Brinqa Supports CTEM Success
Brinqa is a unified exposure management platform uniquely designed to centralize, prioritize, remediate and report on security findings across your environment. The Brinqa platform connects to over 220 tools, including:
- Asset discovery platforms (like Axonius and ServiceNow)
- Vulnerability scanners (like Qualys, Tenable, and Wiz)
- Threat intelligence feeds (like Recorded Future)
- SIEMs and SOARs (like Cortex)
- BAS tools (like CyCognito)
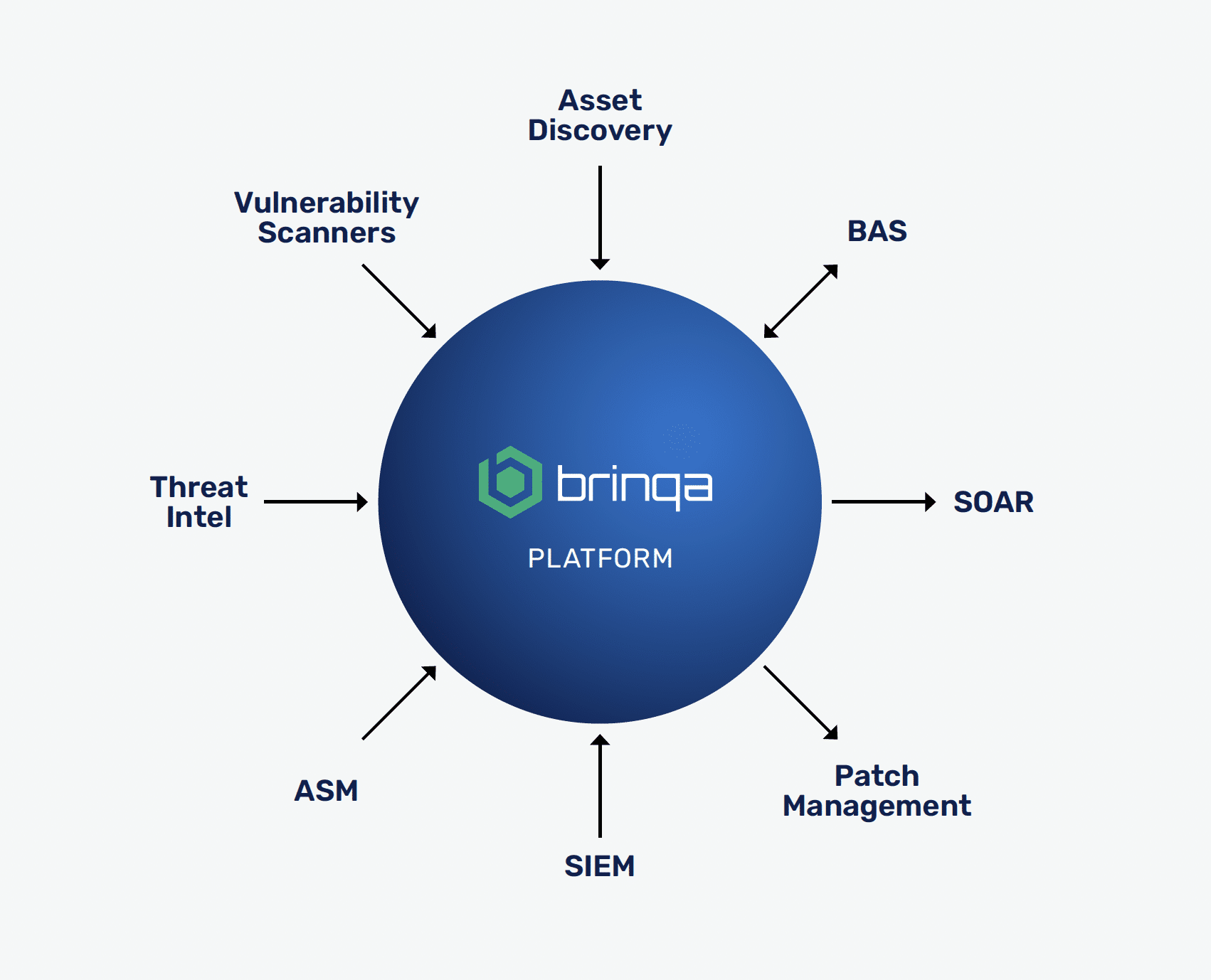
Brinqa brings it all together to provide a single source of truth and turn insight into action. With Brinqa, companies like Nestlé, SAP, and Cambia have reduced remediation time, uncovered blind spots, and focused on the 2% of issues that posed 98% of risk.
Want to Go Deeper?
Download the new white paper, Why Risk-Based Vulnerability Management Should Be at the Center of Continuous Threat Exposure Management, for a deep-dive into the tools, challenges and approaches for maximizing CTEM success.
For more on how Brinqa can enable a comprehensive CTEM approach, request a demonstration today.
Frequently Asked Questions (FAQ)
What is the difference between CTEM and traditional vulnerability management?
Traditional vulnerability management often relies on periodic scanning and static risk scores. CTEM is continuous and dynamic — it evaluates exposures in real time based on context, business impact, and real-world threat intelligence.
Why is risk-based vulnerability management (RBVM) essential for CTEM?
RBVM ensures that remediation efforts focus on the most critical vulnerabilities, not just the most numerous. It combines threat intel, asset value, exploitability, and business impact to prioritize what matters most.
What kinds of tools are involved in a CTEM strategy?
A complete CTEM program may include:
- Asset discovery tools
- Vulnerability scanners
- Threat intelligence platforms
- Attack surface management tools
- Breach and attack simulation (BAS)
- SIEM and SOAR platforms
- RBVM platforms (like Brinqa)
What are the biggest challenges to implementing CTEM?
Common obstacles include:
- Tool sprawl and poor integration
- Incomplete visibility of digital assets
- Resource constraints
- Prioritization overload
- High implementation and licensing costs
How does RBVM help reduce alert fatigue?
RBVM cuts through the noise by surfacing only the vulnerabilities that are both exploitable and impactful. It filters out low-priority issues, reducing the volume of alerts security teams need to triage.
How does Brinqa support CTEM and RBVM?
Brinqa integrates with 220+ security tools to centralize, normalize, and prioritize exposure data. It serves as a control center for CTEM—automating prioritization, orchestration, and remediation workflows at enterprise scale.
What’s the business value of investing in a CTEM approach with RBVM?
Organizations that adopt a CTEM approach with RBVM at the center see:
- Faster remediation from automations and centralized orchestration
- Reduced risk of breaches due to comprehensive asset and vulnerability management
- Lower operational costs through automations
- Better use of security resources through prioritization
- Alignment of security with business priorities from consolidated reporting