Are You Struggling with One of These Top Vulnerability Management Challenges?
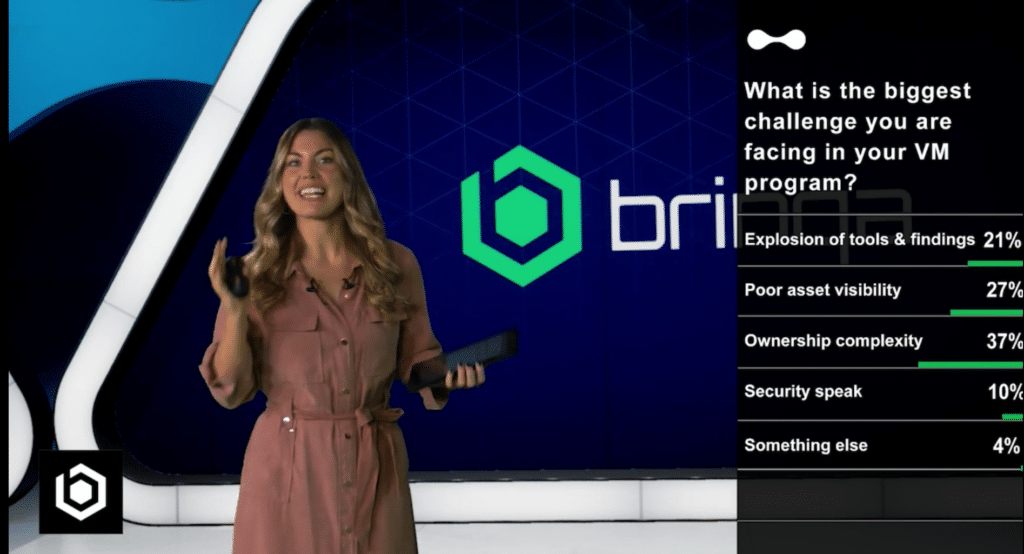
During a recent webinar on the importance of reframing vulnerability management, more than 100 VM professionals responded to the poll question: “What’s the biggest challenge you are facing in your VM program?”
For 85% of respondents, it is one of three top challenges:
According to guest speakers Martin Karel, global security vulnerability management product lead for Nestlé, and Steve Hawkins, director of security architecture and engineering for Cambia Health, these results are consistent with their own experiences.
To help explain why these problems are so pervasive today, here’s a quick history lesson. In the early days of vulnerability management, there was a relatively small scale of IT assets to worry about: endpoints, virtual machines, and network equipment. Then public cloud entered the fray, and managing vulnerabilities across the attack surface became significantly more difficult.
Let’s analyze these survey results and dive into why these challenges are so prevalent — and predictable — among VM programs.
2 out of 3 VM teams struggle with ownership complexity and poor asset visibility
64% — nearly 2/3 of respondents — struggle with ownership complexity (37%) or poor asset visibility (27%) as their top challenge.
While ownership complexity and poor asset visibility were separate choices in the survey, when analyzing these results, we combined the two. Why? Because they are two sides of the same coin. The attack surface has grown dramatically as a direct result of most businesses acting on their digital transformation initiatives.
Poor asset visibility has spawned an entirely new category CAASM — cyber asset attack surface management — as vendors try to overcome the shortcomings of CMDBs. But what makes this the most frequently cited “top challenge” in our survey? Well, vulnerability management teams aren’t starting from scratch. They are dealing with and prioritizing an existing pile of problems.
Common sense dictates that if you know a vulnerable asset exists and you’ve already decided it’s a remediation priority, you will focus on assigning that remediation ticket to an owner. But it never seems to be that simple. CMDBs are notoriously out of date, and security scanners often share findings without much context, and — if that weren’t hard enough — the workforce at large is amid the great talent re-shuffle, which means a lot of tribal knowledge around what assets exist and who owns them has or soon will walk out the door.
1 in 5 VM teams is trying to tame an explosion of tools and findings
In the hierarchy of challenges, while only 21% of respondents cited the explosion of tools and findings as the top challenge for their VM program, many teams still acknowledge it as a significant problem.
There are typically two categories of VM teams in this bucket:
- Teams that have already addressed the visibility and ownership complexity challenges mentioned above and, by doing so, have shined a light on areas in their asset inventories with missing security controls.
- Teams reacting to an audit or pen test report that focused a spotlight on a security controls gap.
While new tools seemingly appear every month that can scan for new vulnerabilities, the reality is many VM teams are still trying to deal with their “known knowns.”
Here’s the thing: Attackers don’t care (and neither do auditors and pen testers). It’s not uncommon for businesses to realize that they have scanning gaps in their code and/or SDLC as identified by their latest compliance audit or pen test. This indicates teams need to do a better job of securing against hardcoded secrets, securing your APIs, or protecting the CI/CD pipeline.
As organizations add new scanning technologies, it becomes increasingly important to figure out how to rationalize these findings consistently alongside findings from existing scanners and programs — and then develop a reliable way to prioritize these risks for remediation.
Overcoming “security speak” is a challenge for 10% of security teams
For many, “security speak” is another problem for VM teams (e.g., ownership complexity, poor asset visibility, and an explosion of tools and findings).
Unlike the CISO, vulnerability management professionals do not directly interact and report to the board of directors, CEO or CIO/CTO, but for 1 in 10 survey respondents overcoming security speak is a challenge.
VM teams are at the mercy of the data to which they have access. Since vulnerability and security findings surface without business context, VM teams have the challenging job of helping business owners, and non-technical stakeholders understand why it’s imperative to resolve these issues promptly (e.g., “Your flagship product or upcoming launch is out of compliance and/or has a vulnerability that is likely to be exploited.”)
These problems are more connected than you might think
We’ve examined the close link between asset visibility and ownership complexity. You might be wondering about the connection between those issues and the explosion of tools/findings or security speak.
It’s obvious why asset visibility and ownership complexity are linked: as you improve your asset visibility, the number of asset owners you must document and navigate grows more complex. Perhaps it’s manually doable at a small scale, but for larger enterprises, navigating this level of complexity begs for technology to help solve the problem.
Similarly, as more and more scans occur to identify various risks, the specific individual or team to whom you need to assign the remediation ticket to address the issue becomes more complicated. Who’s responsible for making that public s3 bucket private? That depends. Is the problem the result of code from an IaC scan or a misconfigured setting detected by your CSPM tool?
What can VM teams do?
Having up-to-date, precise, actionable intel on vulnerabilities is critical to streamlining remediation and helping you communicate with people in different business areas. You need technical precision when trying to remediate issues at the engineering level. You also need breadcrumbs that can map issues back to the business level so you can marshal the resources required to build a strong security posture. As teams mature and overcome their initial challenges of wading through the explosion of tools and findings, poor asset visibility, and ownership complexity, they often need help to up-level their security speak so non-technical stakeholders can understand the risks their business units face.

