Scoping & Discovery:
Ingests, normalizes, and retains data from every connected source. Preserves the relationships, context, and lineage that make downstream intelligence reliable.
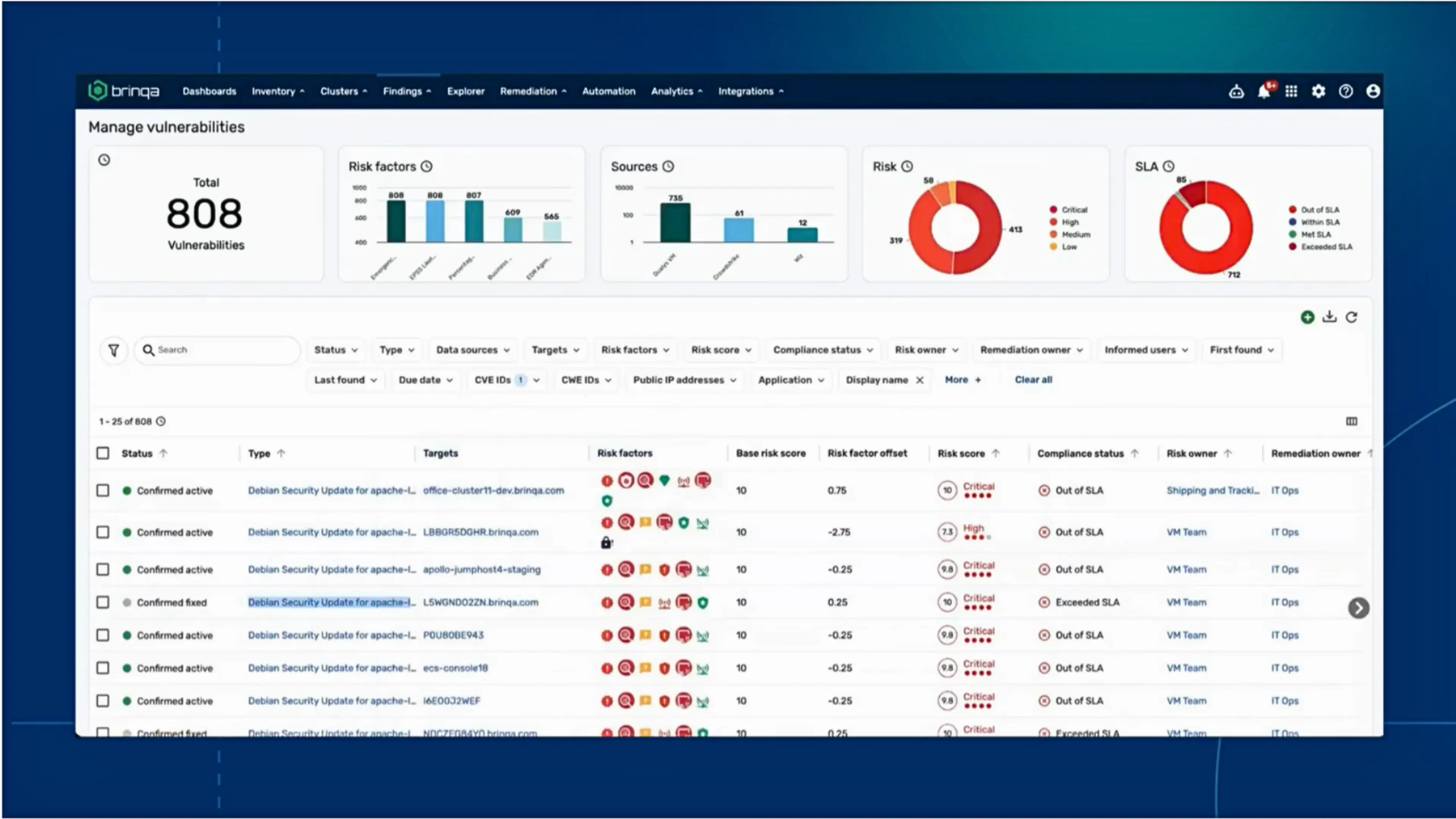
Most enterprises have invested heavily in tooling. The data is flowing – what’s broken is everything that happens after it lands. Findings arrive without the business context needed to make them actionable. The operational impact shows up across every vulnerability management program:
At the core of Brinqa’s Data Layer is the CyberRisk Graph™, a data model built to flex and expand with enterprise complexity.
The Brinqa Platform doesn’t just ingest data; It contextualizes, normalizes, and cleanses exposure data from any source without forcing it into rigid schemas, enabling unified exposure management across your entire environment.
That means every AI recommendation, every prioritization call, and every remediation workflow above it is built on a foundation you can trust.
See how Brinqa preserves relationships and attributes across every exposure record — and why that changes every prioritization decision downstream.
| Before and After | Without a Unified Data Foundation | With the Brinqa Data Layer |
|---|---|---|
Duplicate Findings & Data Normalization | Five findings in five tools for one real vulnerability. Teams spend hours reconciling what should have been one ticket. | The CyberRisk Graph™ normalizes and correlates findings into a single, remediation ticket. |
Ownership & Accountability | Ownership records are missing or stale. Exposures sit in the backlog because nobody is clearly accountable. | The Data Layer preserves relationship context and attribute data, then enables the AI Layer to infer missing ownership from patterns in your data. |
Data Completeness & Flexibility | Rigid schemas discard context on import or prohibit data types and data fields from being ingested. Decisions get made on an incomplete picture of the environment. | Every attribute, relationship, and signal is retained and used for input into the data model. All the data is used to determine ownership, prioritize what matters most and create reports. |
Historical Data & Compliance | Historical data lives in spreadsheets or disconnected systems. Trend analysis and audit support require manual assembly. | BrinqaDL retains years of enriched exposure and remediation data, queryable through the platform or external tools. |
Ingests, normalizes, and retains data from every connected source. Preserves the relationships, context, and lineage that make downstream intelligence reliable.
Operates on the unified data from the CyberRisk Graph – with the ability to overlay historical context from BrinqaDL – to close ownership gaps, deduplicate findings, and surface prioritized risk. Every AI recommendation is only as trustworthy as the data it runs on.
Turns AI-attributed findings and prioritized risk into structured workflows, automated ticketing, and reporting that gives every stakeholder the view they need. Reliable orchestration depends on reliable data.