Data Gaps Are a Security Risk. We Built Something to Close Them.
by Brinqa, Research Team//
AI attribution in exposure management is the automated process of inferring and completing missing or inconsistent asset attributes — including ownership, environment, criticality, and business unit — using machine learning applied locally within a security platform. Accurate attribution is a prerequisite for vulnerability prioritization, remediation routing, and risk-based exposure management.
THE DATA QUALITY PROBLEM
When Ownership Is Missing, Everything Downstream Breaks.

THE DATA QUALITY PROBLEM
When Ownership Is Missing, Everything Downstream Breaks.
Most enterprises can't prioritize or route what they can't attribute, and most attribution is incomplete by default.
Brinqa's analysis of enterprise customer environments reveals that 78% of enterprise assets lack a defined risk owner on average, and 58% of findings have no defined risk owner. When ownership is missing, risk scoring has no business context, remediation tickets stall, and the entire downstream program runs on incomplete data.
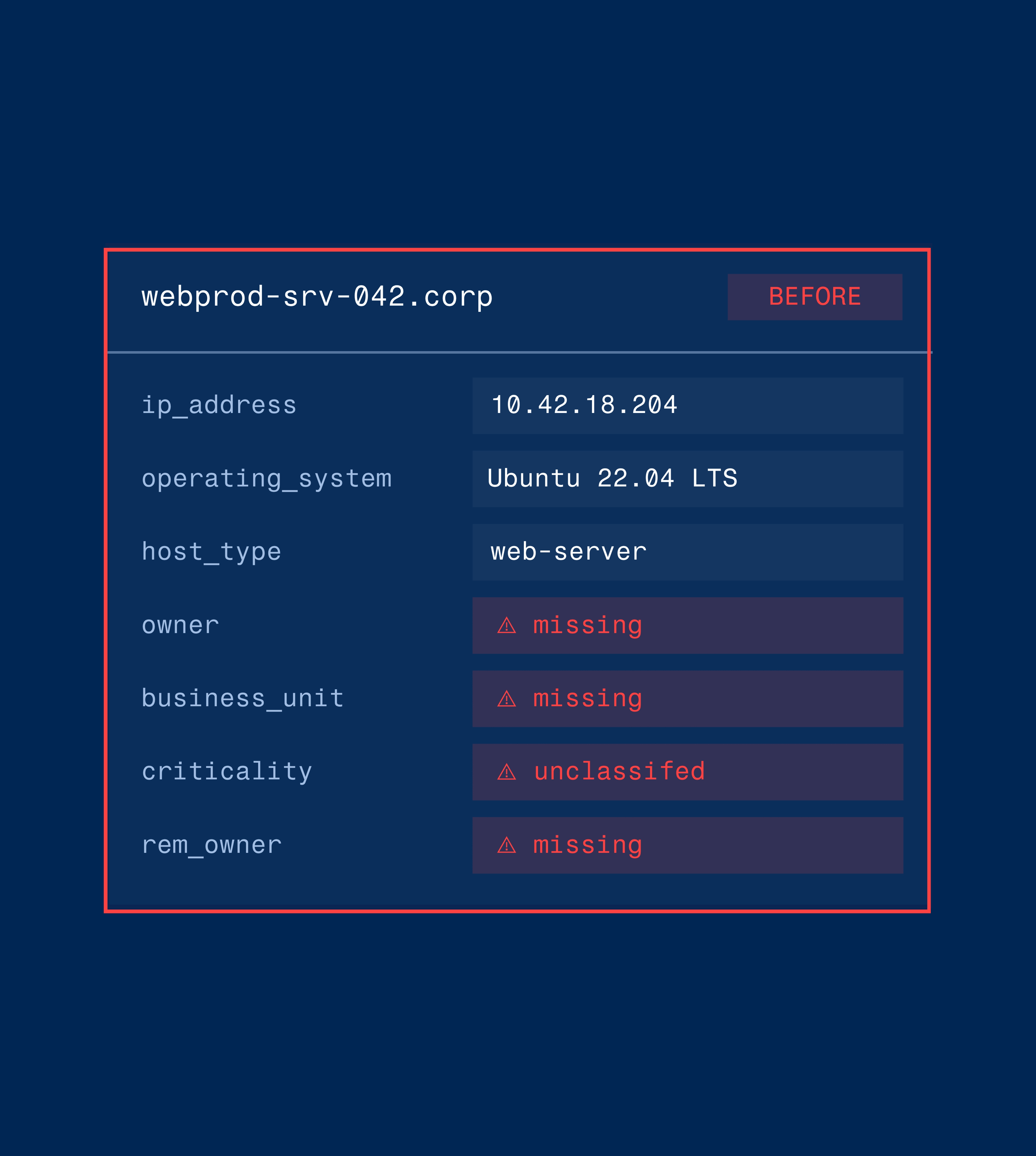
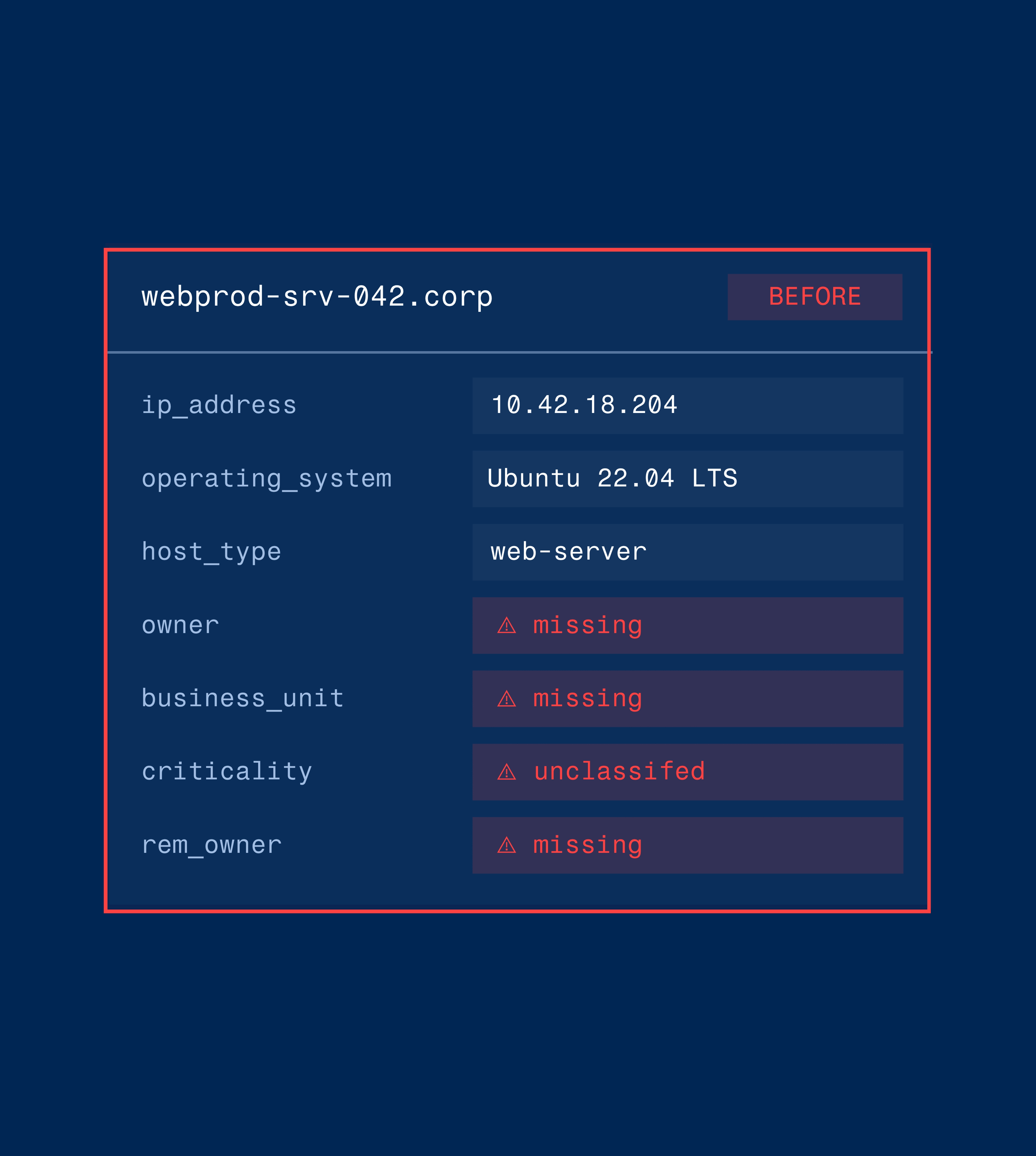
The infographic below shows exactly how this happens, and how the Brinqa AI Attribution Agent resolves it.
Outcomes
What Complete Exposure Data Actually Makes Possible
When every asset, finding, and custom model is fully attributed, risk scoring, remediation routing, and board reporting all work from the same reliable foundation.
- Asset ownership: Missing on 78% of assets on average
- Finding context: 58% of findings have no defined risk owner
- Remediation routing: Manual, slow, frequently stalled
- Risk score accuracy: Built on incomplete data
- Board reporting: Ownership gaps create defensibility risk
You cannot prioritize what you cannot clearly see. You cannot automate what you cannot reliably trust.
Built for Every Team That Depends on Accurate Exposure Data
Defensible ownership coverage metrics for board reporting.
Track ownership coverage over time as a concrete indicator of cyber risk posture improvement.
Risk scores grounded in complete context, not data gaps.
Stop spending cycles chasing ownership before remediation can begin.
Every finding routes to a named owner.
Tickets arrive fully contextualized. SLAs are enforceable because accountability is defined before the work starts.
AI Attribution Agent in Action
See How it Works in the Platform

AI Attribution Agent in Action
See How it Works in the Platform
Administrators configure confidence thresholds, set target attributes, and retain full audit trail visibility into every AI-populated field. The model applies locally within your environment. Your data never leaves your tenant.
See how it fits into Brinqa’s full exposure management platform, and what it means for your program.