Vulnerability management is the process of identifying, assessing, and remediating security weaknesses across systems and applications. It provides the foundation for security programs, but on its own often lacks the context needed to prioritize real-world risk.
Risk-based vulnerability management (RBVM) builds on this by prioritizing vulnerabilities based on exploitability, asset criticality, and business impact — not just severity scores.
The Challenge
Why Vulnerability Risk Management Breaks Down

The Challenge
Why Vulnerability Risk Management Breaks Down
Vulnerability teams are flooded with findings but still struggle to answer basic questions: what actually matters, who owns it, and what needs to be fixed first. Multiple scanners report the same issue differently, severity scores lack context, and ownership is often unclear.
The result is noise, growing backlogs, and remediation efforts that don’t always align to real risk.
How Brinqa Works
How Brinqa Enables Risk-Based Vulnerability Management
Brinqa modernizes vulnerability management by making it repeatable and scalable—unifying findings, assets, threat intelligence, and business context into a single exposure model:
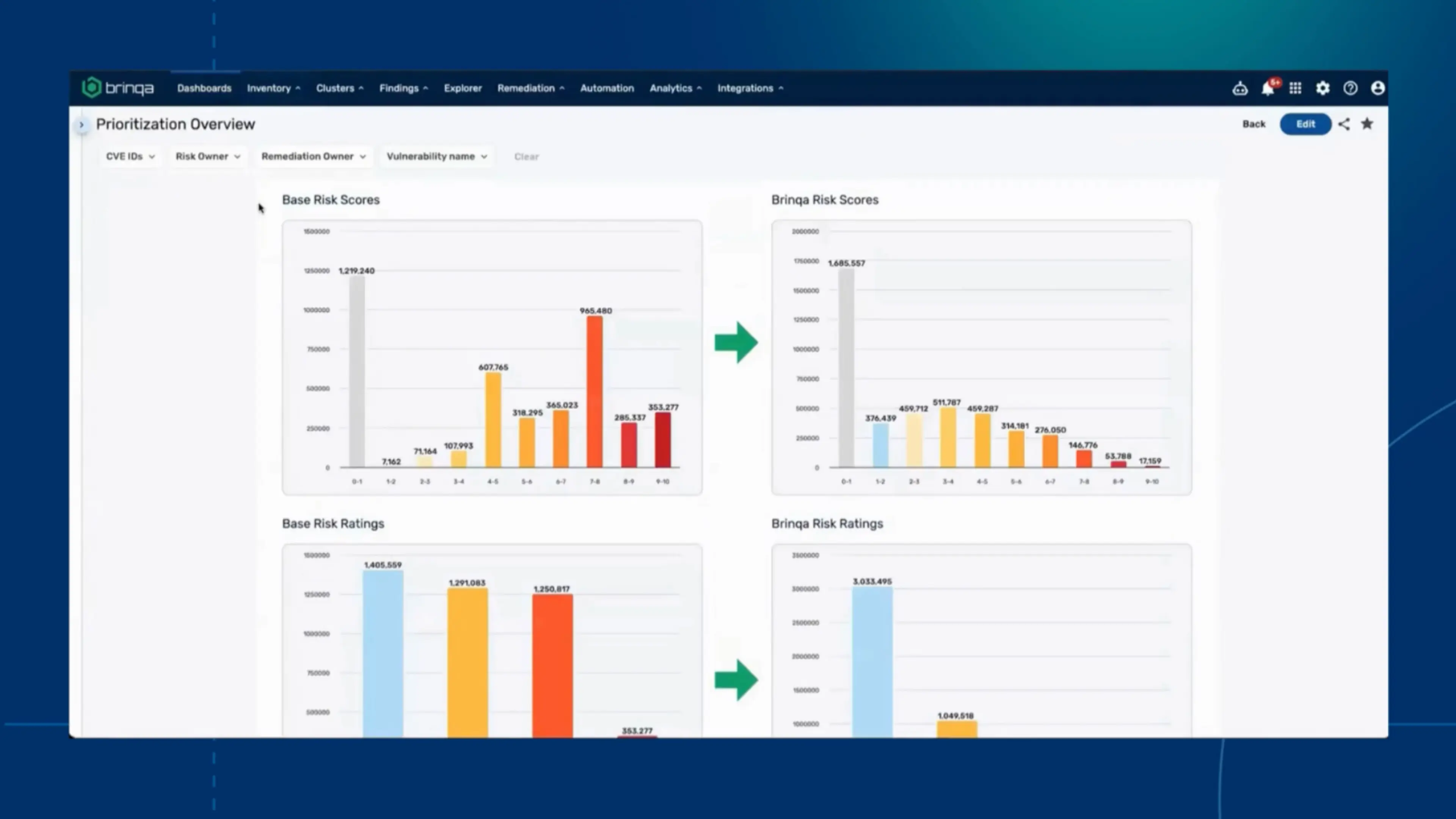
Identify True Critical Vulnerabilities
See how Brinqa focuses remediation effort
Watch how Brinqa applies organizational context to collapse the critical pile — so remediation efforts align to real risk, not raw severity.
Key Capabilities
Platform Capabilities That Power RBVM
Understanding risk based vulnerability management
Vulnerability Management, Explained
Vulnerability management provides visibility into security weaknesses—but prioritization becomes difficult at scale.
Most programs follow a continuous cycle:
- Discover vulnerabilities across assets
- Assess severity (e.g., CVSS)
- Prioritize remediation
- Track and report progress
Result: visibility into issues—but not always clarity on what matters most.
Brinqa at Work
Solutions For Every Member of Your Vulnerability Management Program
CISO & Security Risk Management Leaders

Vulnerability & Exposure Management Leaders

IT, Cloud, & App Security Teams

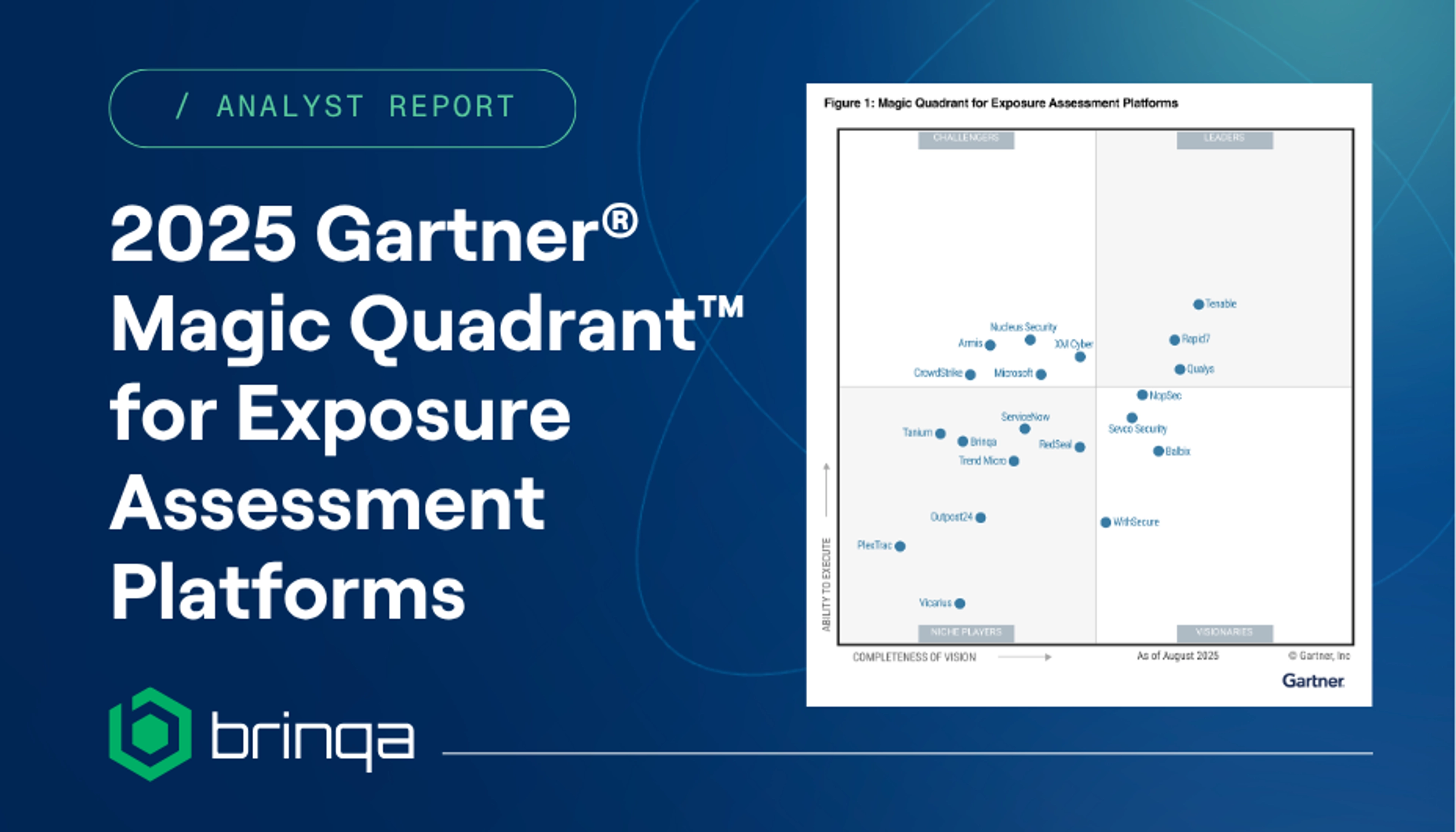

Exposure Management
Three Demos: This Is Context-Driven Exposure Management in Action

