How Claude Security and Brinqa Turn Code Exposures Into Closed Risk
by Brad Hibbert, COO & CSO//12 min read/

Every security team has a version of this story. Thousands of findings, dozens of tools, and somewhere in that pile is the vulnerability that actually matters. It is sitting at severity medium in a service nobody remembered to tag as critical, while lower-risk issues get fixed first because they looked worse on a dashboard. The problem is never the tools. It is that nothing connects what the scanners find to what the business actually cares about.
That is the gap Brinqa exists to close, and it is why Claude Security caught our attention. Anthropic built it directly into Claude Enterprise as a code scanner that reads your GitHub repositories the way a security researcher would rather than a rule engine. Connected to Brinqa, it becomes part of something more complete: findings that arrive with context, get ranked by real business risk, and reach the right developer with prescriptive guidance already attached.
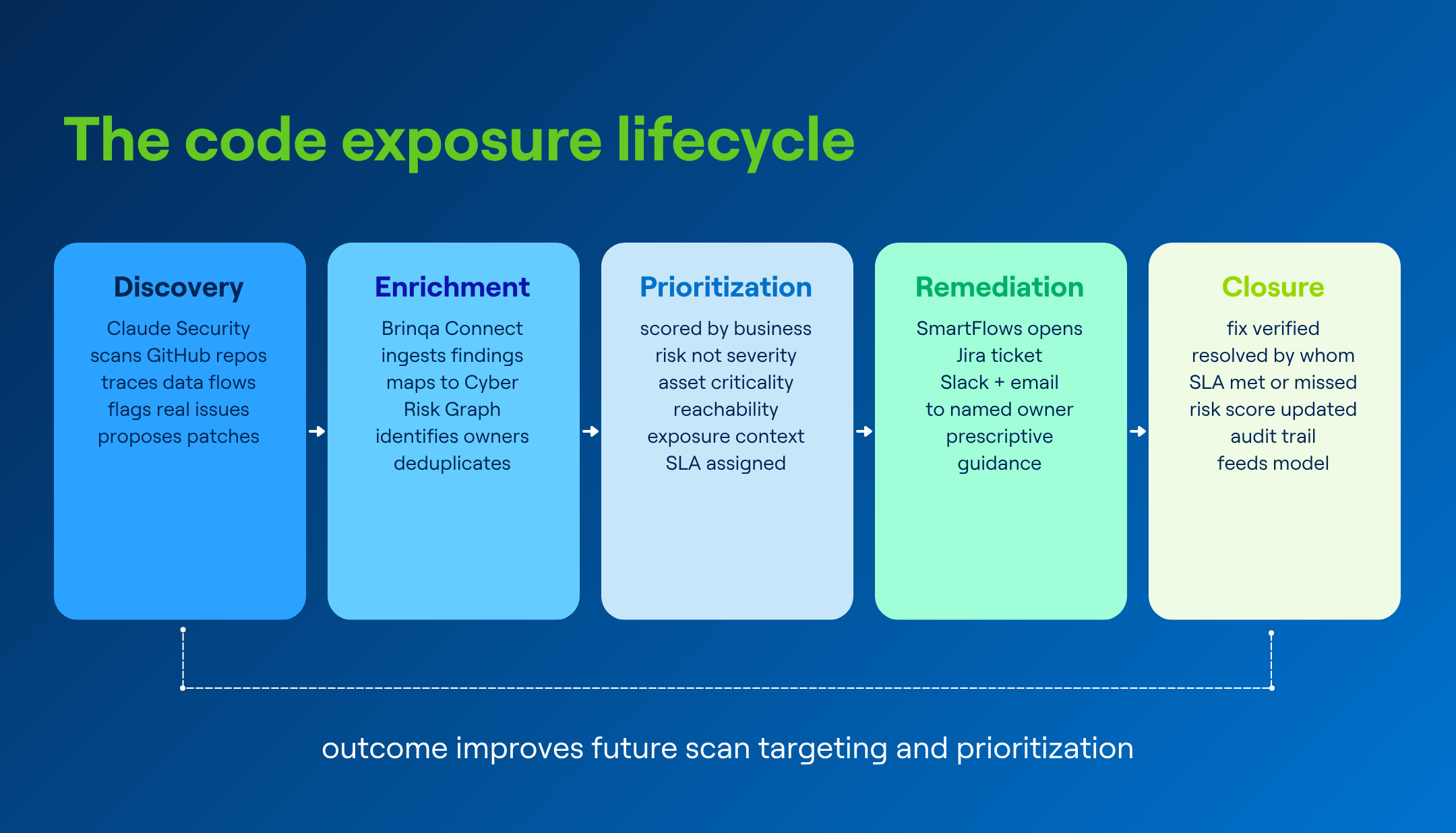
From discovery to verified closure, with every step attributed, SLA-tracked, and feeding back into the prioritization model.
What Claude Security actually does
Claude Security is Anthropic's code scanning tool, built directly into Claude Enterprise. It connects to your GitHub repositories and reviews the source code your development teams write, looking for security vulnerabilities before that code ever reaches production. Think of it as an AI security researcher sitting alongside your developers, reading the same code they write, and flagging real problems rather than generating a list of theoretical risks for someone else to sort through later. Most code scanning tools work by matching patterns against a library of known vulnerability signatures. They are fast and broad but they miss the nuance of how code actually behaves in context. Claude Security traces data flows across files, reads the business logic embedded in the code, and reasons about how an attacker would actually approach the application. Before it surfaces a finding, it runs a verification pass on its own output to filter out noise, so what comes through is a small set of real issues rather than thousands of alerts that need human triage to become useful.
Each finding arrives with the affected file and line, a plain-language explanation of why it matters, and a proposed patch ready for a developer to review and apply. The developer does not need to interpret a scanner alert and figure out what to do next. The work of going from observation to action has already been done.
The gap that needs bridging
Here is where most code scanning pipelines come apart. A scanner produces a finding, the finding goes into a queue, the queue grows, and eventually somebody triages it if the team has time and assigns it a ticket. The ticket sits in Jira next to two hundred others until either a developer fixes it or someone decides it was a false positive and closes it without action. At no point in that process does anyone ask whether the vulnerable code runs on an asset that is internet-exposed, whether it handles authentication or customer PII, whether the service it belongs to is on the critical path for a revenue-generating product, or whether three other scanners are already pointing at the same underlying issue from different angles.
Those are exactly the questions Brinqa's platform exists to answer. The CyberRisk Graph™ already holds the relationships between assets, services, applications, business context, and ownership. SmartFlows, the graphical no-code automation engine inside Brinqa, already knows how to open a ticket, notify the right team in Slack, and send the right people an email with the priority and context attached. All of that becomes significantly more powerful when code exposure findings from Claude Security are flowing into it continuously.
The integration at a glance:
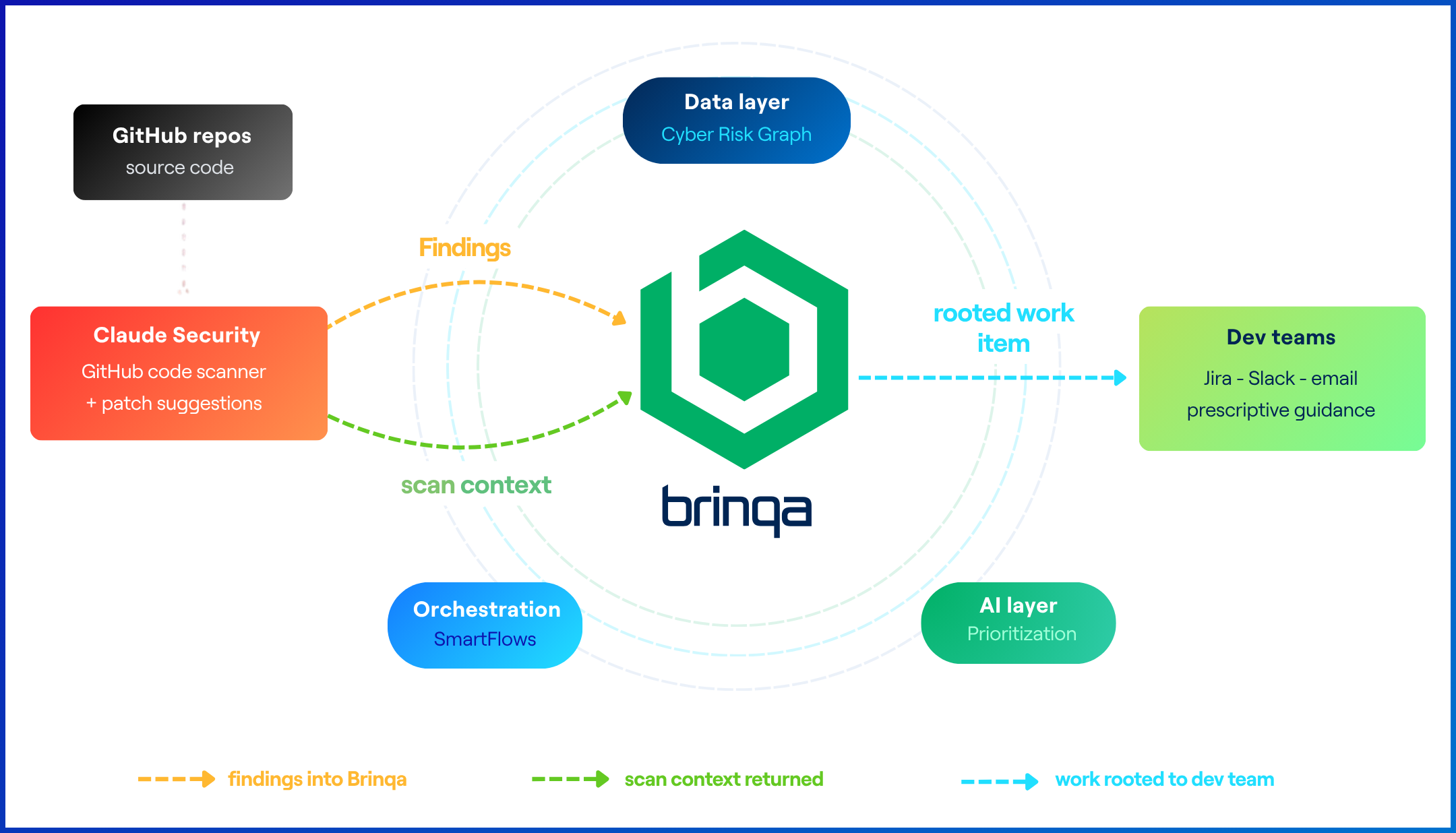
Claude Security findings flow into Brinqa via Brinqa Connect, enriched with business context and routed to development teams through SmartFlows.
How the connection works today
One of the first questions in any integration conversation is whether Brinqa can receive data from a new external source without a lengthy connector build. For Claude Security, the answer is a clear yes, and the mechanism is Brinqa Connect, a shipping capability currently at version 2.1 that exposes an ingress and egress API specifically designed to bring custom data into the Brinqa Platform from any external system.
Brinqa Connect handles API key authentication, supports delta syncs so you are only pulling net-new findings rather than the full dataset on every cycle, and manages rate limiting and timeout retries out of the box. The way it works with Claude Security is that when a scan completes, Claude Security pushes the full findings payload including vulnerability type, severity, affected file and line, repository, and proposed patch to the Brinqa Connect endpoint. That payload lands at the Brinqa Connect API endpoint, the connector picks it up on its next sync cycle, and from that point the findings move through the same normalization, deduplication, and Cyber Risk Graph mapping pipeline as every other source in the platform.
Any joint customer running Claude Enterprise and Brinqa can stand this up through configuration and schema work rather than engineering a new connector from scratch. The path from Claude Security scan to Brinqa-prioritized exposure is available now.
What happens when Claude Security meets the Cyber Risk Graph
Once findings are flowing in through Brinqa Connect, they stop being isolated events and become part of the unified exposure management picture. Brinqa scores them alongside cloud misconfigurations, infrastructure vulnerabilities, and other risks. A code-level injection vulnerability in a public-facing API gets a very different adjusted score than the same class of vulnerability sitting in an internal batch process that runs once a week on a non-networked host. The code is the same. The risk to the business is not, and most code scanning pipelines on their own have no way to make that call.
Deduplication is equally important here. Claude Security, Checkmarx, Snyk, and a penetration test might all flag the same vulnerability in the same file, which without Brinqa would show up as four separate findings driving four separate tickets. With Brinqa's AI deduplication agent in the loop, those collapse into a single exposure record with full attribution across all contributing sources, and your developers fix it once. The end result for the remediation team is a prioritized list of code exposures ordered by actual business risk rather than scanner severity, with ownership routing already resolved and prescriptive guidance attached before the developer even opens it.
Closing the loop through SmartFlows
Where the integration really earns its keep is at the orchestration layer. Once Brinqa has scored and ranked a code exposure, SmartFlows takes over as the execution layer. It opens a Jira ticket for the owning development team with the full context already populated, including the vulnerability, the affected file, the adjusted risk score, the SLA deadline, and prescriptive guidance on how to resolve it. Simultaneously it fires a Slack notification to the right team channel and sends a direct email to the named owner, so the finding lands in front of the right people through whatever channel they actually work in, not just in a queue they will get to eventually.
SmartFlows gets the right information to the right person as fast as possible. The developer does not have to go looking for context. It is already there when the ticket lands.
Closure: completing the loop
Opening a ticket is not the same as fixing a vulnerability. Brinqa tracks what happens after the work is assigned. When the developer merges the fix and closes the ticket, Brinqa records who resolved it, whether it landed within the SLA window, and what the risk score looked like before and after. If the SLA was missed, that is recorded too and the exposure remains open until the fix is verified. The audit trail is complete from the moment Claude Security surfaces the finding to the moment the risk is confirmed resolved.
That closure data feeds back into how Brinqa thinks about future findings. Teams with a strong remediation track record can be trusted with longer SLA windows. Services with a pattern of recurring code issues get flagged as candidates for deeper scan coverage. The vulnerability prioritization model sharpens over time because it has real outcome data to learn from rather than just severity scores and asset tags.
What Brinqa can tell Claude Security
So far this has been about data flowing one way. Claude Security finds something and Brinqa makes sense of it. The more interesting question is what happens when Brinqa starts informing the scanner. Brinqa already knows things about your environment at scan time that Claude Security does not. It knows which repositories map to business-critical services, which applications handle authentication flows or customer data, and which assets are internet-exposed versus buried behind internal network controls. That context, fed back to Claude Security when scans are being configured, is the difference between spending extended scan compute on every repository equally and spending it where a finding would actually change a risk decision.
Claude Security supports scoping scans to specific directories, branches, and modules, and offers a deeper extended scan mode designed for higher-stakes reviews. Brinqa's risk model can drive those decisions, directing extended scans at repositories tied to critical services, running standard scans everywhere else, and routing findings from high-priority repos directly to the front of the queue. The result is scanning effort that is proportional to actual business risk rather than evenly spread across every repository regardless of what it does or who depends on it.
Looking further ahead, Brinqa sees a world where this relationship becomes even more direct. As AI models become more extensible and context-aware, the opportunity is not just to feed findings into a platform or configure scans from outside. It is to connect models directly to the global exposure repository itself, giving them live access to an organization's full risk context at inference time. A model that can query years of normalized, deduplicated exposure data across assets, services, business applications, and remediation history is no longer just vulnerability-aware. It becomes business-aware, reasoning with the same intelligence that security leaders use to make decisions rather than working from the narrow view of a single scan. That is the direction Brinqa is building toward, and Claude Security is an early proof of what becomes possible when the right data meets the right model.
If you are running Claude Enterprise and Brinqa, the path from code exposure to closed risk is available now. Talk to a Brinqa Expert about standing it up.


